A Comprehensive Review of Cyber Security Threats and Protection Techniques
Main Article Content
Abstract
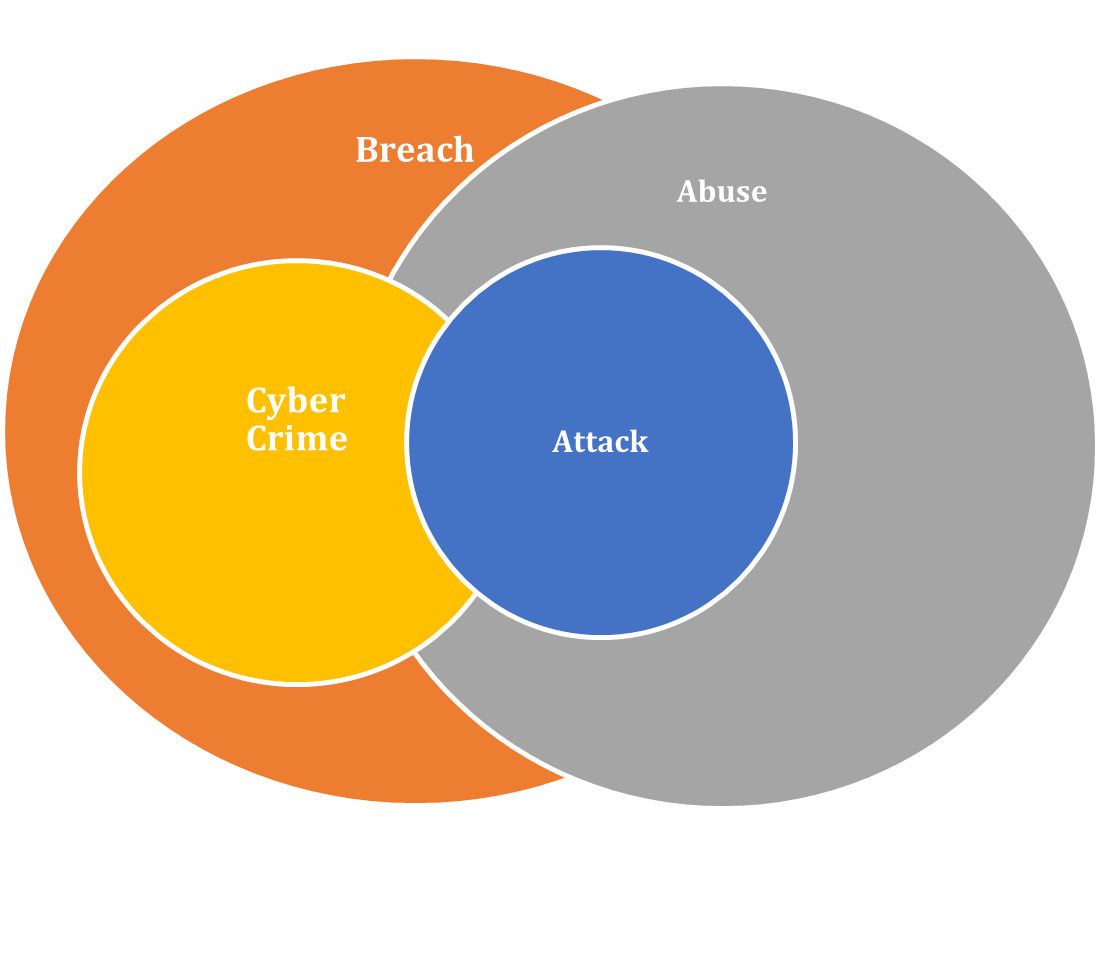
The rapid growth of digital technologies and internet connectivity has significantly transformed how individuals, organisations, and governments operate. However, this digital transformation has also increased the risk of cyber threats and security vulnerabilities. Cyber-attacks, such as malware, phishing, ransomware, and distributed denial-of-service (DDoS), pose serious risks to the confidentiality, integrity, and availability of information systems. As organisations increasingly depend on digital infrastructure, ensuring robust cybersecurity measures has become a critical requirement. This review paper provides a comprehensive analysis of cyber security threats, cybercrime activities, and modern protection techniques used to safeguard digital systems. The study examines the historical development of cyber security, different types of cyber-attacks, and the fundamental principles of information security such as the CIA triad. In addition, the paper discusses the importance of cyber ethics in maintaining responsible and secure digital practices.
Article Details
Section
How to Cite
References
Tan, S., Wang, Y., Li, H., & Zhang, X. (2021). Attack detection design for DC microgrid using an eigenvalue assignment approach. Energy Reports, 7, 469–476.
Waoo, A. A., & Soni, L. N. (2025). Face detection under low-light and low-resolution conditions using CLAHE and a modified CNN. Journal of Neonatal Surgery, 14.
Aghajani, G., & Ghadimi, N. (2018). Multi-objective energy management in microgrids considering renewable energy sources. Energy Reports, 4, 218–225.
Xu, H., Sun, L., Zhai, E., & Huang, J. (2024). Large language models for cyber security: A systematic literature review. arXiv preprint arXiv:2405.04760.
Datar, A., Datar, S., & Soni, L. N. (2017). Implementation of Viola-Jones algorithm-based approach for human face detection. International Journal of Current Engineering and Technology, 7(5), 1819–1823.
Nazario, M., & Alghazzawi, D. (2023). Cyber threat intelligence for security decision-making: A review and research agenda. Computers & Security, 133, 103392.
Shrivastava, P., Gautam, C. S., & Soni, L. N. (2026). Mastering of Machine Learning: From Theory to Deployment. IIP Iterative International Publishers.
Cao, J., Liu, X., Chen, Y., & Wang, L. (2021). Hybrid-triggered security controller design for networked control systems under multiple cyber-attacks. Information Sciences, 548, 69–84.
Gautam, C. S., Pandey, P., & Soni, L. N. (2022). Clustering of big data using genetic algorithm in Hadoop MapReduce. European Chemical Bulletin, 963–973.
Jamal, A., Rahman, M., & Ahmed, K. (2021). Security analysis of cyber-physical systems using machine learning techniques: A review. Materials Today: Proceedings, 45, 3450–3456.
Waoo, A. A., & Soni, L. N. (2023). Unveiling face detection techniques through mathematical insights. European Chemical Bulletin, 12(Special Issue 4), 16895–16903.
Alqarni, M., Alshamrani, A., Khan, R., & Zaman, N. (2024). Economic impact of cyber-attacks and effective cyber risk management strategies. Procedia Computer Science, 228, 392–400.
Reddy, D. B. L. L., Sumathi, M. R., Nanthini, P., & Soni, L. N. (2024). Deep learning algorithm for sentiment analysis of e-commerce. International Journal of Novel Research and Development (IJNRD), 10(5), f70.
Amet, R. (2023). Cyber security vulnerabilities, threats, attacks, and defense solutions: A comprehensive review. Electronics, 12(6), 1333.
Qiu, W., Liu, H., Zhang, J., & Zhao, Y. (2021). Time–frequency based cyber security defense of wide-area control systems. International Journal of Electrical Power & Energy Systems, 132, 107151.
Soni, L. N. (2024). LNSONI Human Face Dataset (Version 1). Mendeley Data. https://doi.org/10.17632/rbczppyyx8.1
Zhang, Y., & Malacaria, P. (2021). Bayesian Stackelberg games for cyber security decision support. Decision Support Systems, 148, 113599.
Kim, Y. S., Lee, H., & Park, J. (2020). Cyber attack probability analysis using AHP and factor analysis. Annals of Nuclear Energy, 149, 107790.
Tosun, O. K. (2021). Cyber-attacks and stock market activity. International Review of Financial Analysis, 76, 101795.
Waoo, A. A., & Soni, L. N. (2026). Hybrid algorithm for human face detection using deep learning method (PhD thesis). AKS University.
Pfleeger, C. P., & Pfleeger, S. L. (2012). Security in Computing (5th ed.). Prentice Hall.
Nguyen, D. C. L., & Golman, D. W. (2021). Development of cybercrime legislation in Pacific Island countries. Computer Law & Security Review, 40, 105521.
Sarada, V., Sharma, S., Rajput, G., Gupta, D., & Soni, L. N. (2026). Management perspectives on knowledge-driven culture: The role of AI and IoT in innovation and governance. Scientific Culture, 12(2.1), 1182–1187.
Katrakazas, C., Quddus, M., Chen, W., & Deka, L. (2020). Cyber security and its impact on connected vehicle safety. Advances in Transport Policy and Planning, 73–94.
Cybersecurity and Infrastructure Security Agency (CISA). (2023). Cyber Safety Review Board: Year in Review 2023.
Ferrag, M. A., et al. (2024). Generative AI in cyber security: A comprehensive review.
Mendes, C., & Rios, T. N. (2023). Explainable artificial intelligence in cyber security. arXiv preprint.
Vasoya, S., Bhavsar, K., & Patel, N. (2022). A systematic review on ransomware attacks. arXiv preprint.
Podder, P., et al. (2021). Artificial neural networks in cyber security. arXiv preprint.
Lee, I. (2020). IoT cyber security and cyber risk management framework. Future Internet, 12(9), 157.
Sharma, P., & Gupta, R. (2025). Artificial intelligence driven cyber threat detection. IEEE Access, 13, 45612–45630.
IBM Security. (2024). Cost of a Data Breach Report 2024. IBM Corporation.
Soni, L., & Waoo, A. (2023). A review of recent advances methodologies for face detection. International Journal of Current Engineering and Technology, 13(2), 86–92.
Datar, A., Datar, S., & Soni, L. N. (2017). Face detection of African origin people and newborn infants using Viola-Jones algorithm. International Journal of Computer Trends and Technology, 51(2).
Holmes, W., Bialik, M., & Fadel, C. (2019). Artificial Intelligence in Education.
Soni, L. N., & Waoo, A. A. (2026). LNS Occluded and Low-Light Human Face Detection Dataset (Version 3). Mendeley Data. https://doi.org/10.17632/s57wnx78vh.3
Soni, L. N., Waoo, A. A., Agrawal, A., & Vishwakarma, N. (2024). Detecting partial human faces using a hybrid deep learning model. Journal of the Maharaja Sayajirao University of Baroda, 58(1 VIII), 1–8.
Waoo, A. A., & Soni, L. N. (2024). Improving night vision with infrared and visible light sensor fusion. Journal of the Maharaja Sayajirao University of Baroda, 58(1 VIII), 1–8.